 We have prepared AWS Certified Security - Specialty (SCS-C03) certification sample questions to make you aware of actual exam properties. This sample question set provides you with information about the Security Specialty exam pattern, question formate, a difficulty level of questions and time required to answer each question. To get familiar with AWS Certified Security - Specialty exam, we suggest you try our Sample AWS SCS-C03 Certification Practice Exam in simulated AWS certification exam environment.
We have prepared AWS Certified Security - Specialty (SCS-C03) certification sample questions to make you aware of actual exam properties. This sample question set provides you with information about the Security Specialty exam pattern, question formate, a difficulty level of questions and time required to answer each question. To get familiar with AWS Certified Security - Specialty exam, we suggest you try our Sample AWS SCS-C03 Certification Practice Exam in simulated AWS certification exam environment.
To test your knowledge and understanding of concepts with real-time scenario based AWS SCS-C03 questions, we strongly recommend you to prepare and practice with Premium AWS Security Specialty Certification Practice Exam. The premium AWS Security Specialty certification practice exam helps you identify topics in which you are well prepared and topics in which you may need further training to achieving great score in actual AWS Certified Security - Specialty exam.
AWS SCS-C03 Sample Questions:
- Logic tier – RESTful API accessed from the presentation tier through HTTPS, protected by the security group logic-sg
- Data tier – SQL Server database accessed over port 1433 from the logic tier, protected by the security group data-sg
(Select THREE.)
a) presentation-sg: Allow ports 80 and 443 from 0.0.0.0/0
b) data-sg: Allow port 1433 from presentation-sg
c) data-sg: Allow port 1433 from logic-sg
d) presentation-sg: Allow port 1433 from data-sg
e) logic-sg: Allow port 443 from presentation-sg
f) logic-sg: Allow port 443 from 0.0.0.0/0
Which solution meets the requirement with the LEAST risk and effort?
a) Use Amazon CloudWatch Logs to capture all logs, write an AWS Lambda function that parses the log file, and move sensitive data to a different log.
b) Use Amazon CloudWatch Logs with two log groups, with one for each application, and use an AWS IAM policy to control access to the log groups, as required.
c) Aggregate logs into one file, then use Amazon CloudWatch Logs, and then design two CloudWatch metric filters to filter sensitive data from the logs.
d) Add logic to the application that saves sensitive data logs on the Amazon EC2 instances' local storage, and write a batch script that logs into the Amazon EC2 instances and moves sensitive logs to a secure location.
a) Change the IAM permissions by applying PutBucketPolicy permissions.
b) Verify that the policy has the same name as the bucket name. If not, make it the same.
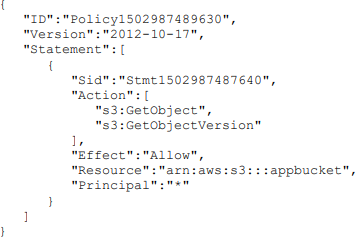
c) Change the resource section to "arn:aws:s3:::appbucket/*".
d) Add an s3:ListBucket action.
a) Review the user's IAM permissions and delete any unrecognized or unauthorized resources.
b) Delete the user, review Amazon CloudWatch Logs in all regions, and report the abuse.
c) Delete or rotate the user’s key, review the AWS CloudTrail logs in all regions, and delete any unrecognized or unauthorized resources.
d) Instruct the user to remove the key from the GitHub submission, rotate keys, and re-deploy any instances that were launched.
(Select TWO.)
a) Add the aws:sourceVpce condition to the AWS KMS key policy referencing the company's VPC endpoint ID.
b) Remove the VPC internet gateway from the VPC and add a virtual private gateway to the VPC to prevent direct, public internet connectivity.
c) Create a VPC endpoint for AWS KMS with private DNS enabled.
d) Use the KMS Import Key feature to securely transfer the AWS KMS key over a VPN.
e) Add the following condition to the AWS KMS key policy: "aws:SourceIp": "10.0.0.0/16".
The following policy was assigned to the role assumed by the Lambda function:
"Version": "2012-10-17",
"Statement": [
{
"Sid": "Dynamo-1234567",
"Action": [
"dynamodb:GetItem"
],
"Effect": "Allow",
"Resource": "*"
}
}
Which least-privilege policy addition would allow this function to log properly?
a) {
"Sid": "Logging-12345",
"Resource": "*",
"Action": [
"logs:*"
],
"Effect": "Allow"
}
b) {
"Sid": "Logging-12345",
"Resource": "*",
"Action": [
"logs:CreateLogStream"
],
"Effect": "Allow"
}
c) {
"Sid": "Logging-12345",
"Resource": "*",
"Action": [
"logs:CreateLogGroup",
"logs:CreateLogStream",
"logs:PutLogEvents"
],
"Effect": "Allow"
}
d) {
"Sid": "Logging-12345",
"Resource": "*",
"Action": [
"logs:CreateLogGroup",
"logs:CreateLogStream",
"logs:DeleteLogGroup",
"logs:DeleteLogStream",
"logs:getLogEvents",
"logs:PutLogEvents"
],
"Effect": "Allow"
}
- Data must be encrypted in transit.
- Data must be encrypted at rest.
- The bucket must be private, but if the bucket is accidentally made public, the data must remain confidential.
Which combination of steps would meet the requirements?
(Select TWO.)
a) Enable AES-256 encryption using server-side encryption with Amazon S3-managed encryption keys (SSE-S3) on the S3 bucket.
b) Enable default encryption with server-side encryption with AWS KMS-managed keys (SSE-KMS) on the S3 bucket.
c) Add a bucket policy that includes a deny if a PutObject request does not include aws:SecureTransport.
d) Add a bucket policy with aws:SourceIp to allow uploads and downloads from the corporate intranet only.
e) Enable Amazon Macie to monitor and act on changes to the data lake's S3 bucket.
Which steps must be taken to meet the retention needs in a scalable, cost-effective way?
a) Enable AWS CloudTrail logging across all accounts to a centralized Amazon S3 bucket with versioning enabled. Set a lifecycle policy to move the data to Amazon Glacier daily, and expire the data after 90 days.
b) Enable AWS CloudTrail logging across all accounts to S3 buckets. Set a lifecycle policy to expire the data in each bucket after 7 years.
c) Enable AWS CloudTrail logging across all accounts to Amazon Glacier. Set a lifecycle policy to expire the data after 7 years.
d) Enable AWS CloudTrail logging across all accounts to a centralized Amazon S3 bucket. Set a lifecycle policy to move the data to Amazon Glacier after 90 days, and expire the data after 7 years.
Which network troubleshooting steps should be taken to resolve the issue?
(Select TWO.)
a) Check to see if the application servers are in a private subnet or public subnet.
b) Check the route tables for the application server subnets for routes to the VPC peering connection.
c) Check the NACLs for the database subnets for rules that allow traffic from the internet.
d) Check the database security groups for rules that allow traffic from the application servers.
e) Check to see if the database VPC has an internet gateway
a) To keep an eye on what the employees on your network are doing.
b) To ensure there are no dropped packets or high latency.
c) To be alerted to unusual traffic entering and exiting your network as a potential security event.
d) To know if access has been made to your private S3 buckets.
Answers:
|
Question: 01 |
Question: 02 |
Question: 03 |
Question: 04 |
Question: 05 |
|
Question: 06 |
Question: 07 |
Question: 08 |
Question: 09 |
Question: 10 |
Note: Please update us by writing an email on feedback@vmexam.com for any error in AWS Certified Security - Specialty certification exam sample questions
